The recent data breach involving the Royal Mail Group has stirred discussions across the logistics and cybersecurity sectors. Allegations of a royal mail data leak and a significant royal mail data breach have raised concerns over the security of data handled by major organizations. This article examines the breach, reviews Royal Mail Group’s response, and discusses its implications for the industry and consumers.

Background of the Incident
On March 31, a user of the dark web forum BreachForum going by the name 'GHNA', claimed that they had successfully breached Royal Mail. The breach has been traced back to Spectos GmbH, a third-party data collection and analytics provider for Royal Mail. Despite this incident, Royal Mail has assured that its operations and services continue to function without disruption.
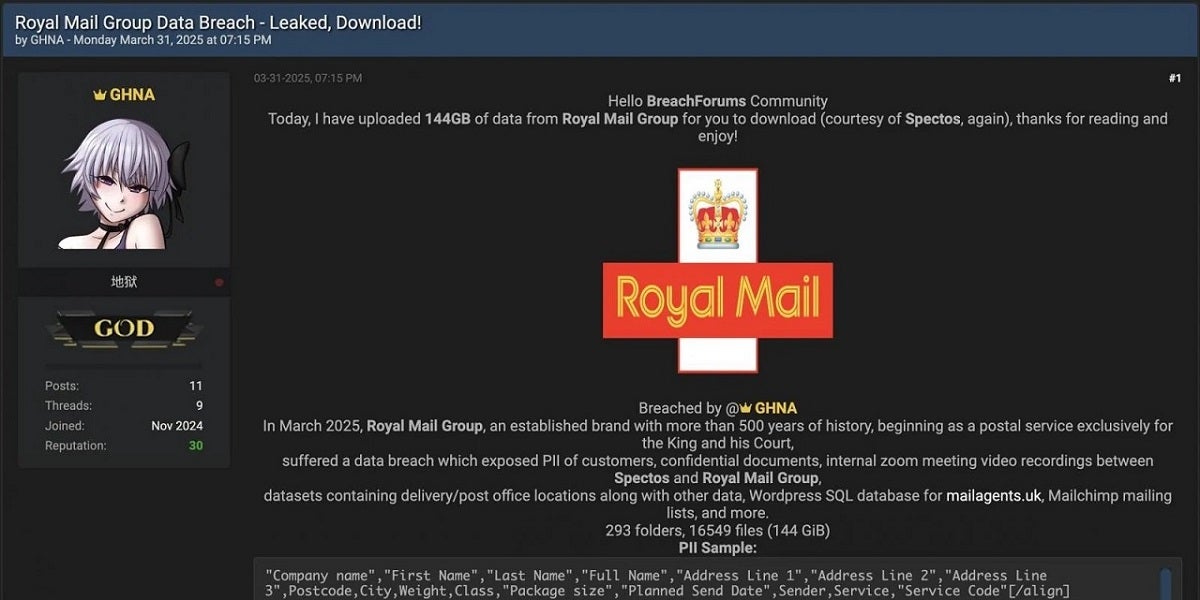
Royal Mail leak on BreachForums. Source: BleepingComputer
Spectos confirmed in a statement to BleepingComputer that its systems were compromised on March 29, and the attackers gained access to customer data. The threat actor has leaked approximately 144GB of data, sparking concerns over the security of customer information and internal operations. This breach highlights vulnerabilities within third-party relationships, an area where many large organizations, including Royal Mail, are increasingly at risk.
Historically, similar incidents in the logistics and postal sectors have shown that a security gap in one vendor can expose an entire network. The Royal Mail Group incident reinforces the need for robust cybersecurity measures that extend beyond a company’s internal systems to every external partner involved in data processing.
Details of the Data Breach
The breach exposed several types of sensitive information, including:
- Customer Personal Information: Data such as names, addresses, postal codes, and shipping details.
- Internal Communications: Confidential internal data, including digital meeting records.
- Operational Data: Information on delivery routes and backend SQL databases.
- Marketing Infrastructure: Data extracted from mailing list exports via platforms like Mailchimp.
Cybersecurity experts suggest that vulnerabilities—such as outdated software and weak access controls at Spectos—could have been exploited by cybercriminals. This incident underscores the importance of regular security audits, timely updates, and comprehensive vendor management practices.
Royal Mail Group’s Response
Royal Mail Group responded quickly to the breach. The company confirmed that, despite the data leak, its operational services remain unaffected and continue to function normally. In collaboration with Spectos, Royal Mail Group is working on a full-scale forensic investigation to assess the scope of the compromise and to enhance security measures for the future. This cooperative response highlights the challenges of managing cybersecurity in an ecosystem that relies heavily on third-party vendors.
Cybersecurity Analysis and Industry Implications
The royal mail data breach not only raises concerns for Royal Mail Group but also sends a clear message to the logistics and postal industries. The incident serves as a wake-up call for organizations to review and strengthen their cybersecurity practices. Companies must enforce robust security protocols and conduct regular vulnerability assessments to minimize risks from third-party partners.
For the industry, the breach brings forward several implications:
- Increased Regulatory Oversight: Enhanced data protection regulations could result in stricter enforcement and higher penalties for non-compliance.
- Consumer Privacy Risks: The exposure of personal data may lead to identity theft and fraud, prompting the need for vigilant monitoring by customers.
- Operational and Financial Repercussions: While immediate operations may not be affected, long-term risks include potential disruption in service delivery and reputational damage.
Businesses are encouraged to implement multi-layered security strategies, including real-time threat detection, encryption of sensitive data, and periodic employee training on cybersecurity best practices. For consumers, it is advisable to update passwords regularly, enable multi-factor authentication, and monitor financial statements for unusual activity.
Actionable Recommendations for Stakeholders
To prevent such breaches, the following measures are recommended:
For Businesses:
- Conduct regular audits of third-party vendor security.
- Install real-time monitoring and intrusion detection systems.
- Update software and security patches without delay.
- Strengthen internal cybersecurity policies and train employees on potential threats.
For Consumers:
- Use strong, unique passwords for online accounts.
- Enable two-factor authentication where available.
- Regularly review bank and credit reports to identify any suspicious activity.
Adopting these proactive measures will help minimize the risks associated with data breaches and enhance overall trust in digital operations.
Conclusion
The Royal Mail Group data breach illustrates the growing challenges in cybersecurity, especially regarding third-party vendor relationships. While Royal Mail Group maintains that there has been no immediate impact on its operations, the incident serves as a significant reminder for all organizations to bolster their cybersecurity defenses. Continuous review and enhancement of security measures are essential to protect sensitive data and maintain consumer trust in an ever-evolving digital landscape.
For organizations, this incident further emphasizes the need to invest in advanced cybersecurity solutions and ensure comprehensive data protection across all levels of operation.
Frequently Asked Questions
On March 29, 2025, unauthorized access was detected at Spectos, a partner of Royal Mail Group. A threat actor then leaked 144GB of data, including sensitive customer information and internal communications.
The leaked data included customer personal information (names, addresses, postal codes), internal communications (including video recordings), operational data (delivery routes, SQL databases), and marketing data (mailing list exports).
Royal Mail Group has stated that the breach did not impact their core operations, and all services remain unaffected despite the leak.
Royal Mail Group and Spectos are collaborating on a forensic investigation and enhancing their security protocols to prevent future breaches. They continue to work on strengthening third-party vendor security measures.
Businesses should implement regular security audits, advanced threat detection, and strict vendor management protocols. Consumers can protect themselves by using strong passwords, enabling multi-factor authentication, and monitoring their financial accounts regularly.





