1. Summary
| Vulnerability Name | Windows Internet Key Exchange (IKE) Protocol Extensions Remote Code Execution Vulnerability (CVE-2022-34721) |
|---|---|
| Component Name | Internet Key Exchange (IKE) Protocol Extensions |
| Affected Versions | IKEv1 Affecting:
|
| Vulnerability Type | Remote Code Execution Vulnerability |
| Severity | CVSS v3 Base Score 9.8 (Critical) |
| Exploitability | Attack Vector: Network Attack Complexity: Low Privileges Required: None User Interaction: None |
| Impact | Confidentiality Impact: High Integrity Impact: High Availability Impact: High |
2. About the Vulnerability
2.1 Introduction
Internet Key Exchange (IKE) is secure key management protocol used to set up a secure and authenticated communications channel between two devices over a virtual private network (VPN). Specifically, IKE uses Internet Protocol Security (IPsec) to set up security associations (SA) that define the security policies for communication.
Internet Key Exchange (IKE) Protocol Extensions are extensions that provide additional capabilities to IKE.
2.2 Summary
CVE-2022-34721 is a remote code execution vulnerability in Internet Key Exchange version 1 (IKEv1). An unauthenticated attacker could send a specially crafted IP packet to a target machine that is running Windows and has IPSec enabled, which could enable a remote code execution exploitation.
3. Affected Versions
IKEv1
Affecting:
Windows 7 for 32-bit Systems Service Pack 1
Windows 7 for x64-based Systems Service Pack 1
Windows 8.1 for 32-bit systems
Windows 8.1 for x64-based systems
Windows RT 8.1
Windows 10 Version 1607 for 32-bit Systems
Windows 10 Version 1607 for x64-based Systems
Windows 10 Version 1809 for 32-bit Systems
Windows 10 Version 1809 for ARM64-based Systems
Windows 10 Version 1809 for x64-based Systems
Windows 10 Version 20H2 for 32-bit Systems
Windows 10 Version 20H2 for ARM64-based Systems
Windows 10 Version 20H2 for x64-based Systems
Windows 10 Version 21H1 for 32-bit Systems
Windows 10 Version 21H1 for ARM64-based Systems
Windows 10 Version 21H1 for x64-based Systems
Windows 10 Version 21H2 for 32-bit Systems
Windows 10 Version 21H2 for ARM64-based Systems
Windows 10 Version 21H2 for x64-based Systems
Windows 10 for 32-bit Systems
Windows 10 for x64-based Systems
Windows 11 for ARM64-based Systems
Windows 11 for x64-based Systems
Windows Server 2008 R2 for x64-based Systems Service Pack 1
Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
Windows Server 2008 for 32-bit Systems Service Pack 2
Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for x64-based Systems Service Pack 2
Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
Windows Server 2012
Windows Server 2012 (Server Core installation)
Windows Server 2012 R2
Windows Server 2012 R2 (Server Core installation)
Windows Server 2016
Windows Server 2016 (Server Core installation)
Windows Server 2019
Windows Server 2019 (Server Core installation)
Windows Server 2022
Windows Server 2022 (Server Core installation)
Windows Server 2022 Datacenter: Azure Edition (Hotpatch)
Note: Only systems with the IKE and AuthIP IPsec Keying Modules running are vulnerable to this attack.
Run either of the following commands to check the running status of this service:
PS: C:\> Get-Service Ikeext
OR
Cmd: C:\> sc query ikeext
4. Solutions
4.1 Remediation Solutions
4.1.1 Check the System Patch Installation
1) Run "systeminfo" in a CMD window and it will display a list of details about the system, including what patches are installed as shown below.
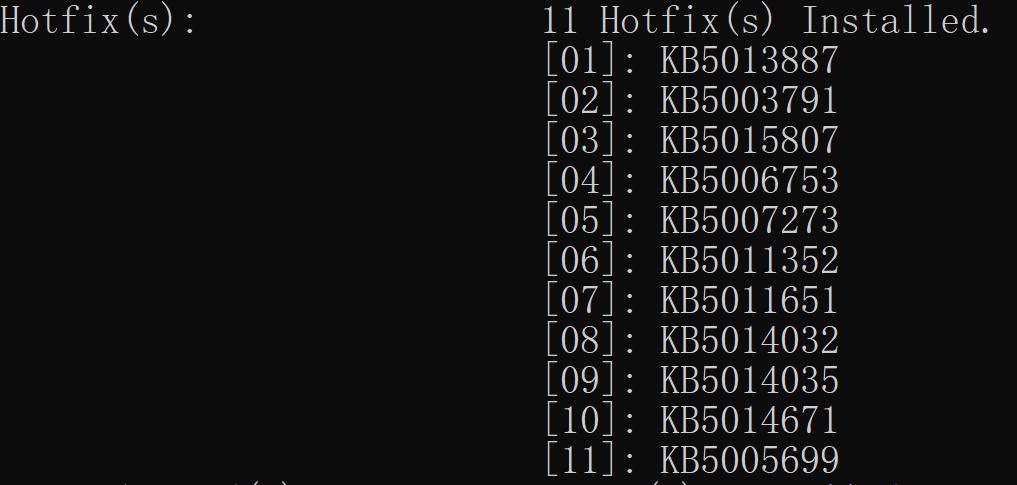
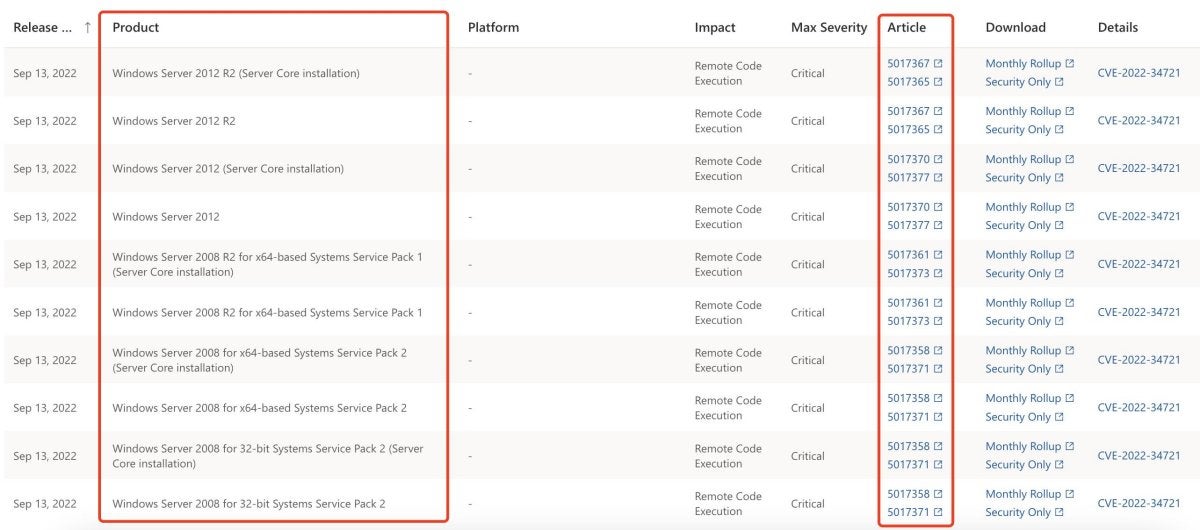
2) Check if the patch corresponding to your OS is installed. Patches for affected OS versions can be found in the link below: https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2022-34721
3) If the patch is not installed, proceed to "4.1.2 Microsoft Solution" to download and install the patch.
4.1.2 Microsoft Solution
Microsoft has released a patch for affected OS versions to fix this vulnerability. Please download the patch corresponding to the affected OS from the following link: https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2022-34721
5. Reference
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2022-34721
https://nvd.nist.gov/vuln/detail/CVE-2022-34721#toggleConfig1
6. Learn More
Sangfor FarSight Labs researches the latest cyberthreats and unknown zero-day vulnerabilities, alerting customers to potential dangers to their organizations, and providing real-time solutions with actionable intelligence. Sangfor FarSight Labs works with other security vendors and the security community at large to identify and verify global cyberthreats, providing fast and easy protection for customers.





