Summary
| Vulnerability Name | Ingress NGINX Controller Remote Code Execution (CVE-2025-1974) |
Released on | March 27, 2025 |
Affected Component | Ingress NGINX Controller |
Affected Versions | Versions earlier than 1.11.5 Versions earlier than 1.12.1 |
Vulnerability Type | Code execution |
Exploitation Condition |
|
Impact | Exploitation difficulty: easy. Attackers can remotely execute code without authorization. Severity: high. Attackers can remotely execute code without authorization. |
Official Solution | Available |
About the Vulnerability
Component Introduction
Ingress NGINX Controller is an NGINX-based ingress controller used to implement Ingress resources in Kubernetes environments.
Vulnerability Description
On March 27, 2025, Sangfor FarSight Labs received notification of the Ingress NGINX Controller Remote Code Execution (CVE-2025-1974) vulnerability, classified as critical in threat level.
This vulnerability enables unauthenticated attackers to inject code for remote code execution by exploiting configuration vulnerabilities when Ingress NGINX Controller handles Ingress objects. This may potentially lead to sensitive information leakage in Kubernetes and server compromises.
Affected Versions
Ingress NGINX Controller with a version earlier than 1.11.5 and 1.12.1 will be affected.
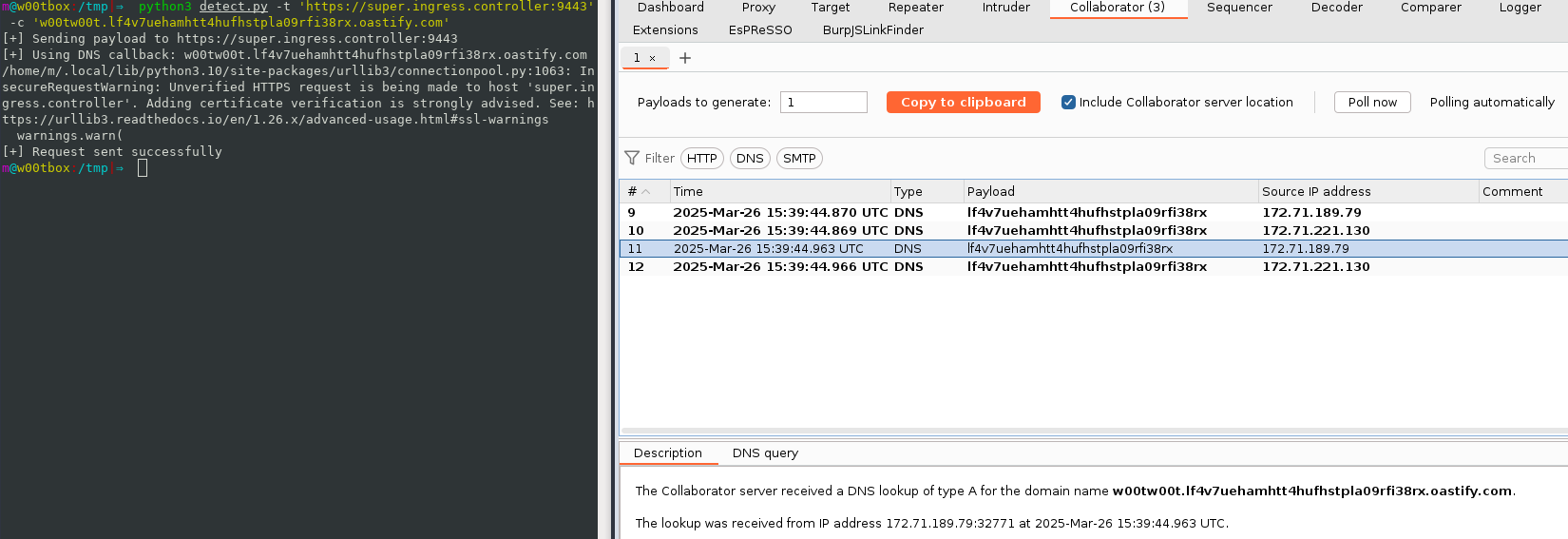
Vulnerability Reproduction
Sangfor FarSight Labs has reproduced the vulnerability.
Solutions
Remediation Solutions
Official Solution
The latest version has been officially released to fix the vulnerability. Affected users are advised to update the version of Ingress NGINX Controller to 1.11.5 or 1.12.1.
Download link: https://github.com/kubernetes/ingress-nginx/releases
Sangfor Solutions
Vulnerability Detection
The following Sangfor services can proactively detect CVE-2025-1974 vulnerabilities and quickly identify vulnerability risks in batches:
Sangfor Host Security: The corresponding detection solution will be released on March 30, 2025. The rule ID is SF-2025-00362.
Sangfor TSS: The corresponding detection solution will be released on March 31, 2025. The rule ID is SF-2025-00999.
Sangfor Cyber Guardian Platform: The corresponding detection solution will be released on March 31, 2025. The rule ID is SF-2025-00999. In this case, make sure that Sangfor Cyber Guardian Platform is integrated with Sangfor TSS.
Sangfor XDR: The corresponding detection solution will be released on March 30, 2025. The rule ID is SF-2025-00362. In this case, make sure that Sangfor XDR is integrated with Sangfor Host Security.
Vulnerability Monitoring
The following Sangfor services support CVE-2025-1974 vulnerability monitoring, and can quickly identify affected assets and the impact business scope in real time through traffic collection:
Cyber Command: The corresponding monitoring solution will be released on April 03, 2025. The rule ID is 11027469.
Sangfor Cyber Guardian Platform: The corresponding monitoring solution will be released on April 03, 2025. The rule ID is 11027469. In this case, make sure that Sangfor Cyber Guardian Platform is integrated with Cyber Command.
Sangfor XDR: The corresponding monitoring solution will be released on April 03, 2025. The rule ID is 11027469.
Vulnerability Protection
The following Sangfor services can effectively block CVE-2025-1974 exploits:
Network Secure: The corresponding protection solution will be released on April 03, 2025. The rule ID is 11027469.
Sangfor Web Application Firewall: The corresponding protection solution will be released on April 03, 2025. The rule ID is 11027469.
Sangfor Cyber Guardian Platform: The corresponding protection solution will be released on April 03, 2025. The rule ID is 11027469. In this case, make sure that Sangfor Cyber Guardian Platform is integrated with Network Secure.
Sangfor XDR: The corresponding protection solution will be released on April 03, 2025. The rule ID is 11027469. In this case, make sure that Sangfor XDR is integrated with Network Secure.
Timeline
On March 27, 2025, Sangfor FarSight Labs received notification of the Ingress NGINX Controller Remote Code Execution (CVE-2025-1974) vulnerability.
On March 27, 2025, Sangfor FarSight Labs released a vulnerability alert.
References
https://www.wiz.io/blog/ingress-nginx-kubernetes-vulnerabilities
https://kubernetes.io/blog/2025/03/24/ingress-nginx-cve-2025-1974/
Learn More
Sangfor FarSight Labs researches the latest cyber threats and unknown zero-day vulnerabilities, alerting customers to potential dangers to their organizations, and providing real-time solutions with actionable intelligence. Sangfor FarSight Labs works with other security vendors and the security community at large to identify and verify global cyber threats, providing fast and easy protection for customers.





