Summary
On December 11, 2024, Microsoft released its December 2024 Security Updates, which included patches for a total of 72 CVEs, a decrease of 20 compared to the previous month.
In terms of vulnerability severity, there were 16 vulnerabilities marked as "Critical," and 55 vulnerabilities were marked as "Important/High" level vulnerabilities. Regarding the types of vulnerabilities, there were primarily 31 remote code execution vulnerabilities, 27 privilege escalation vulnerabilities, and 7 information disclosure vulnerabilities.
Statistics
Vulnerability Trend
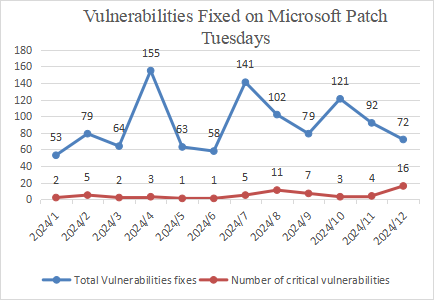
Figure 1 Vulnerabilities Patched by Microsoft in the Last 12 Months
On the whole, Microsoft released 72 patches in December 2024, including patches for 16 critical vulnerability patches.
Based on Microsoft's historical vulnerability disclosures and the specific circumstances of this year, Sangfor FarSight Labs estimates that Microsoft will announce more vulnerabilities in the coming January in comparison to December. We expect a figure of approximately 80 vulnerabilities.
Comparison of Vulnerability Trends
The following figure shows the number of patches released by Microsoft in the month of December from 2021 to 2024.
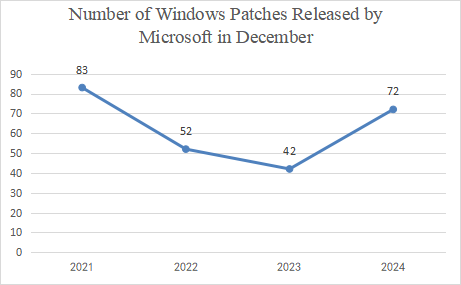
Figure 2 Number of Windows Patches Released by Microsoft in December from 2021 to 2024
The following figure shows the trend and number of vulnerabilities at different severity levels addressed by Microsoft in December from 2021 to 2024.
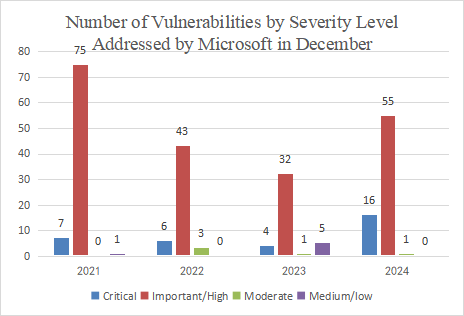
Figure 3 Number of Vulnerabilities by Severity Level Addressed by Microsoft in December from 2021 to 2024
The following figure shows the number of vulnerabilities by type addressed by Microsoft in December from 2021 to 2024.
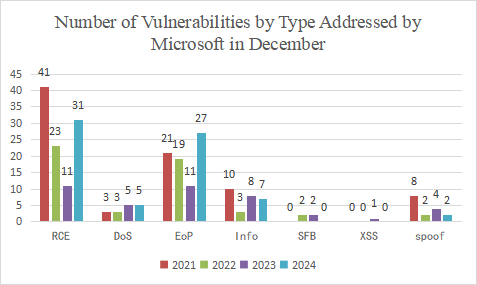
Figure 4 Number of Vulnerabilities by Type Addressed by Microsoft in December from 2021 to 2024
Data source: Microsoft security updates
Compared to last year, there has been an increase in terms of the number of vulnerabilities of this year while the number of vulnerabilities addressed by Microsoft in December 2024 has also increased. A total of 72 vulnerability patches, including 16 critical ones, have been reported this month.
Compared to last year, the number of vulnerabilities at the Critical level addressed by Microsoft has increased, and that of vulnerabilities at the Important/High level has also increased. 55 vulnerabilities at the Important/High level have been addressed, an increase of about 72%, and 16 vulnerabilities at the Critical level have been addressed, an increase of about 300%.
In terms of Vulnerability Type, the number of RCE and EoP vulnerabilities has increased, and that of DoS vulnerabilities remains the same as last year. However, we should remain highly vigilant because, when combined with social engineering techniques, attackers can exploit RCE vulnerabilities to take over an entire LAN and launch attacks.
Details of Key Vulnerabilities
Analysis
Windows Generic Log File System Driver Privileges Escalation Vulnerability (CVE-2024-49138)
The Generic Log File System is a general-purpose logging file system that can be accessed from kernel mode or user-mode applications to build a high-performance transaction log.
A privilege escalation vulnerability exists within it, which attackers can exploit to gain higher privileges on the target system. This vulnerability is known to be exploited in the wild, and after assessment, it is considered critical in threat level. We recommend that users promptly update the Microsoft security patches.
Windows Lightweight Directory Access Protocol (LDAP) Remote Code Execution Vulnerability (CVE-2024-49112)
The Lightweight Directory Access Protocol is an open, neutral, industry-standard application protocol that provides access control and maintenance of distributed directory information through IP protocols. Directory services play a significant role in the development of internal networks and the sharing of users, systems, networks, services, and applications with internet programs. For example, directory services may provide an organized set of records, often with hierarchical structures, such as a company's email directory.
A remote code execution vulnerability exists within it, which attackers can exploit to execute arbitrary code on the target system. This vulnerability is known to be exploited in the wild, and after assessment, it is considered critical in threat level. We recommend that users promptly update the Microsoft security patches.
Affected Versions
| Vulnerability Name | Affected Versions |
|---|---|
| Windows Generic Log File System Driver Privileges Escalation Vulnerability (CVE-2024-49138) | Windows Server 2008 R2 for x64-based Systems Service Pack 1 Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) Windows Server 2008 for x64-based Systems Service Pack 2 Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) Windows Server 2008 for 32-bit Systems Service Pack 2 Windows Server 2016 (Server Core installation) Windows Server 2016 Windows 10 Version 1607 for x64-based Systems Windows 10 Version 1607 for 32-bit Systems Windows 10 for x64-based Systems Windows 10 for 32-bit Systems Windows Server 2025 Windows 11 Version 24H2 for x64-based Systems Windows 11 Version 24H2 for ARM64-based Systems Windows Server 2022, 23H2 Edition (Server Core installation) Windows 11 Version 23H2 for x64-based Systems Windows 11 Version 23H2 for ARM64-based Systems Windows Server 2025 (Server Core installation) Windows 10 Version 22H2 for 32-bit Systems Windows 10 Version 22H2 for ARM64-based Systems Windows 10 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for ARM64-based Systems Windows 10 Version 21H2 for x64-based Systems Windows 10 Version 21H2 for ARM64-based Systems Windows 10 Version 21H2 for 32-bit Systems Windows Server 2022 (Server Core installation) Windows Server 2022 Windows Server 2019 (Server Core installation) Windows Server 2019 Windows 10 Version 1809 for x64-based Systems Windows 10 Version 1809 for 32-bit Systems Windows Server 2012 R2 (Server Core installation) Windows Server 2012 R2 Windows Server 2012 (Server Core installation) Windows Server 2012 Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) |
| Windows Web Query Tagging Security Feature Bypass Vulnerability (CVE-2024-38217) | Windows 10 for x64-based Systems Windows 10 for 32-bit Systems Windows Server 2025 Windows 11 Version 24H2 for x64-based Systems Windows 11 Version 24H2 for ARM64-based Systems Windows Server 2022, 23H2 Edition (Server Core installation) Windows 11 Version 23H2 for x64-based Systems Windows 11 Version 23H2 for ARM64-based Systems Windows Server 2025 (Server Core installation) Windows 10 Version 22H2 for 32-bit Systems Windows 10 Version 22H2 for ARM64-based Systems Windows 10 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for ARM64-based Systems Windows 10 Version 21H2 for x64-based Systems Windows 10 Version 21H2 for ARM64-based Systems Windows 10 Version 21H2 for 32-bit Systems Windows Server 2022 (Server Core installation) Windows Server 2022 Windows Server 2019 (Server Core installation) Windows Server 2019 Windows 10 Version 1809 for x64-based Systems Windows 10 Version 1809 for 32-bit Systems Windows Server 2012 R2 (Server Core installation) Windows Server 2012 R2 Windows Server 2012 (Server Core installation) Windows Server 2012 Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Ser ver Core installation) Windows Server 2008 R2 for x64-based Systems Service Pack 1 Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) Windows Server 2008 for x64-based Systems Service Pack 2 Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) Windows Server 2008 for 32-bit Systems Service Pack 2 Windows Server 2016 (Server Core installation) Windows Server 2016 Windows 10 Version 1607 for x64-based Systems Windows 10 Version 1607 for 32-bit Systems |
Solutions
Official Solution
Microsoft has released patches for affected applications. Affected users can install the corresponding security updates according to the system versions:
Download Links:
- https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-49138
- https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-49112
References
https://msrc.microsoft.com/update-guide/releaseNote/2024-Dec
Timeline
On December 11, 2024, Microsoft released a security bullet.
On December 11, 2024, Sangfor FarSight Labs released a vulnerability alert.





