Summary
On March 12, 2025, Microsoft released its March 2025 Security Updates, which included patches for a total of 58 CVEs, a decrease of 9 compared to the previous month.
In terms of vulnerability severity, there were 6 vulnerabilities marked as "Critical," and 51 vulnerabilities were marked as "Important/High" level vulnerabilities. Regarding the types of vulnerabilities, there were primarily 24 remote code execution vulnerabilities, 22 privilege escalation vulnerabilities, and 4 information disclosure vulnerabilities.
Statistics
Vulnerability Trend
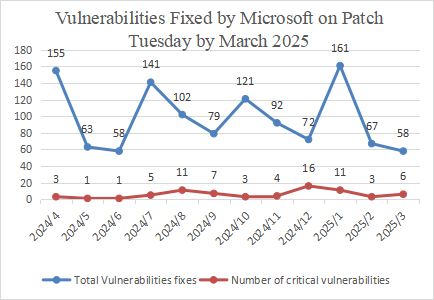
Figure 1 Vulnerabilities Patched by Microsoft in the Last 12 Months
On the whole, Microsoft released 58 patches in March 2025, including patches for 6 critical vulnerability patches.
Based on Microsoft's historical vulnerability disclosures and the specific circumstances of this year, Sangfor FarSight Labs estimates that Microsoft will announce more vulnerabilities in the coming April in comparison to March. We expect a figure of approximately 80 vulnerabilities.
Comparison of Vulnerability Trends
The following figure shows the number of patches released by Microsoft in the month of March from 2022 to 2025.
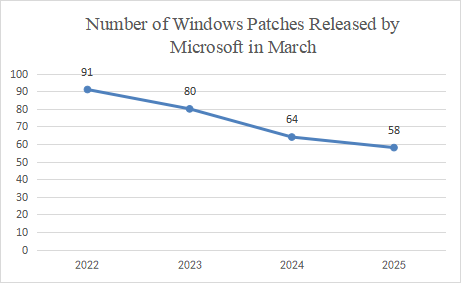
Figure 2 Number of Windows Patches Released by Microsoft in March from 2022 to 2025
The following figure shows the trend and number of vulnerabilities at different severity levels addressed by Microsoft in March from 2022 to 2025.
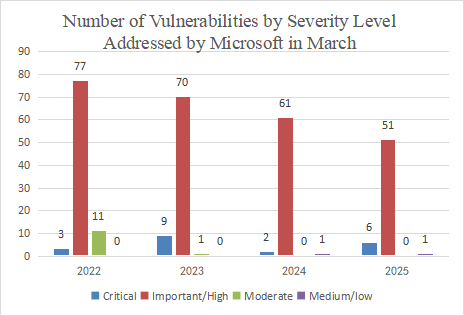
Figure 3 Number of Vulnerabilities by Severity Level Addressed by Microsoft in March from 2022 to 2025
The following figure shows the number of vulnerabilities by type addressed by Microsoft in March from 2022 to 2025.

Figure 4 Number of Vulnerabilities by Type Addressed by Microsoft in March from 2022 to 2025
Data source: Microsoft security updates
Compared to last year, there has been a decrease in terms of the number of vulnerabilities of this year. The number of vulnerabilities addressed by Microsoft in March 2025 has decreased. A total of 58 vulnerability patches, including 6 critical ones, have been reported this month.
Compared to last year, the number of vulnerabilities at the Critical level addressed by Microsoft has increased, and that of vulnerabilities at the Important/High level has decreased. 51 vulnerabilities at the Important/High level have been addressed, a decrease of about 16%, and 6 vulnerabilities at the Critical level have been addressed, an increase of about 200%.
In terms of Vulnerability Type, the number of RCE vulnerability has increased; the number of DoS vulnerabilities and EoP vulnerabilities has decreased. However, we should remain highly vigilant because, when combined with social engineering techniques, attackers can exploit RCE vulnerabilities to take over an entire LAN and launch attacks.
Details of Key Vulnerabilities
Analysis
Windows NTFS Remote Code Execution Vulnerability (CVE-2025-24993)
NTFS is a modern file system developed by Microsoft, introduced with Windows NT in 1993. It supports large files (up to 8PB), logging, permission control, and encryption, and is known for its high reliability and fault tolerance. NTFS is a core storage solution for Windows.
A remote code execution vulnerability exists within it, which attackers can exploit to execute arbitrary code on the target system. This vulnerability is known to be exploited in the wild, and after assessment, it is considered critical in threat level. We recommend that users promptly update the Microsoft security patches.
Windows NTFS Information Disclosure Vulnerability (CVE-2025-24991)(CVE-2025-24984)
NTFS is a modern file system developed by Microsoft, introduced with Windows NT in 1993. It supports large files (up to 8PB), logging, permission control, and encryption, and is known for its high reliability and fault tolerance. NTFS is a core storage solution for Windows.
An information disclosure vulnerability exists within it, which attackers can exploit to gain unauthorized information on the target system. This vulnerability is known to be exploited in the wild, and after assessment, it is considered critical in threat level. We recommend that users promptly update the Microsoft security patches.
Windows FAST FAT File System Driver Remote Code Execution Vulnerability (CVE-2025-24985)
The FAT file system is a file allocation table system developed by Microsoft. It supports FAT12, FAT16, and FAT32 formats and is used in DOS, early versions of Windows, and embedded devices. At its core is the File Allocation Table (FAT), which manages storage space through clusters. The FAT file system is known for its cross-platform compatibility and is widely used in mobile storage devices such as SD cards and USB drives.
A remote code execution vulnerability exists within it, which attackers can exploit to execute arbitrary code on the target system. This vulnerability is known to be exploited in the wild, and after assessment, it is considered critical in threat level. We recommend that users promptly update the Microsoft security patches.
Microsoft Management Console Security Feature Bypass Vulnerability (CVE-2025-26633)
The Microsoft Management Console (MMC) is a unified platform for managing Windows system tools. It integrates various plug-ins (such as Device Manager and Group Policy) to manage hardware, software, and network components. Users can launch it by running the mmc command or opening .msc files, and it supports custom console configurations.
A security feature bypass vulnerability exists within it, which attackers can exploit to ypass the security features on the target system to perform actions outside the specified regulations on the target system. This vulnerability is known to be exploited in the wild, and after assessment, it is considered critical in threat level. We recommend that users promptly update the Microsoft security patches.
Windows Win32 Kernel Subsystem Privilege Escalation Vulnerability (CVE-2025-24983)
The Windows Win32 kernel subsystem is a core component of the operating system. It includes the kernel-mode driver win32k.sys (which handles window management and graphics rendering) and the user-mode component csrss.exe (which manages processes). It provides GUI support through user32.dll and gdi32.dll, and is responsible for the system's graphical interface, input response, and application interaction.
A privilege escalation vulnerability exists within it, which attackers can exploit to gain higher privileges on the target system. This vulnerability is known to be exploited in the wild, and after assessment, it is considered critical in threat level. We recommend that users promptly update the Microsoft security patches.
Affected Versions
| Vulnerability Name | Affected Versions |
| Windows NTFS Remote Code Execution Vulnerability (CVE-2025-24993) | Windows 10 for 32-bit Systems Windows 10 for x64-based Systems Windows 10 Version 1607 for 32-bit Systems Windows 10 Version 1607 for x64-based Systems Windows 10 Version 1809 for 32-bit Systems Windows 10 Version 1809 for x64-based Systems Windows 10 Version 21H2 for 32-bit Systems Windows 10 Version 21H2 for ARM64-based Systems Windows 10 Version 21H2 for x64-based Systems Windows 10 Version 22H2 for 32-bit Systems Windows 10 Version 22H2 for ARM64-based Systems Windows 10 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for ARM64-based Systems Windows 11 Version 22H2 for x64-based Systems Windows 11 Version 23H2 for ARM64-based Systems Windows 11 Version 23H2 for x64-based Systems Windows 11 Version 24H2 for ARM64-based Systems Windows 11 Version 24H2 for x64-based Systems Windows Server 2008 for 32-bit Systems Service Pack 2 Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) Windows Server 2008 for x64-based Systems Service Pack 2 Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) Windows Server 2008 R2 for x64-based Systems Service Pack 1 Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Ser ver Core installation) Windows Server 2012 Windows Server 2012 (Server Core installation) Windows Server 2012 R2 Windows Server 2012 R2 (Server Core installation) Windows Server 2016 Windows Server 2016 (Server Core installation) Windows Server 2019 Windows Server 2019 (Server Core installation) Windows Server 2022 Windows Server 2022 (Server Core installation) Windows Server 2022, 23H2 Edition (Server Core installation) Windows Server 2025 Windows Server 2025 (Server Core installation) |
| Windows NTFS Information Disclosure Vulnerability (CVE-2025-24991) | Windows 10 for 32-bit Systems Windows 10 for x64-based Systems Windows 10 Version 1607 for 32-bit Systems Windows 10 Version 1607 for x64-based Systems Windows 10 Version 1809 for 32-bit Systems Windows 10 Version 1809 for x64-based Systems Windows 10 Version 21H2 for 32-bit Systems Windows 10 Version 21H2 for ARM64-based Systems Windows 10 Version 21H2 for x64-based Systems Windows 10 Version 22H2 for 32-bit Systems Windows 10 Version 22H2 for ARM64-based Systems Windows 10 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for ARM64-based Systems Windows 11 Version 22H2 for x64-based Systems Windows 11 Version 23H2 for ARM64-based Systems Windows 11 Version 23H2 for x64-based Systems Windows 11 Version 24H2 for ARM64-based Systems Windows 11 Version 24H2 for x64-based Systems Windows Server 2008 for 32-bit Systems Service Pack 2 Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) Windows Server 2008 for x64-based Systems Service Pack 2 Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) Windows Server 2008 R2 for x64-based Systems Service Pack 1 Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Ser ver Core installation) Windows Server 2012 Windows Server 2012 (Server Core installation) Windows Server 2012 R2 Windows Server 2012 R2 (Server Core installation) Windows Server 2016 Windows Server 2016 (Server Core installation) Windows Server 2019 Windows Server 2019 (Server Core installation) Windows Server 2022 Windows Server 2022 (Server Core installation) Windows Server 2022, 23H2 Edition (Server Core installation) Windows Server 2025 Windows Server 2025 (Server Core installation) |
| Windows NTFS Information Disclosure Vulnerability (CVE-2025-24984) |
Windows 10 for x64-based Systems Windows 10 Version 1607 for 32-bit Systems Windows 10 Version 1607 for x64-based Systems Windows 10 Version 1809 for 32-bit Systems Windows 10 Version 1809 for x64-based Systems Windows 10 Version 21H2 for 32-bit Systems Windows 10 Version 21H2 for ARM64-based Systems Windows 10 Version 21H2 for x64-based Systems Windows 10 Version 22H2 for 32-bit Systems Windows 10 Version 22H2 for ARM64-based Systems Windows 10 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for ARM64-based Systems Windows 11 Version 22H2 for x64-based Systems Windows 11 Version 23H2 for ARM64-based Systems Windows 11 Version 23H2 for x64-based Systems Windows 11 Version 24H2 for ARM64-based Systems Windows 11 Version 24H2 for x64-based Systems Windows Server 2012 Windows Server 2012 (Server Core installation) Windows Server 2012 R2 Windows Server 2012 R2 (Server Core installation) Windows Server 2016 Windows Server 2016 (Server Core installation) Windows Server 2019 Windows Server 2019 (Server Core installation) Windows Server 2022 Windows Server 2022 (Server Core installation) Windows Server 2022, 23H2 Edition (Server Core installation) Windows Server 2025 Windows Server 2025 (Server Core installation) |
| Windows FAST FAT File System Driver Remote Code Execution Vulnerability (CVE-2025-24985) | Windows 10 for 32-bit Systems Windows 10 for x64-based Systems Windows 10 Version 1607 for 32-bit Systems Windows 10 Version 1607 for x64-based Systems Windows 10 Version 1809 for 32-bit Systems Windows 10 Version 1809 for x64-based Systems Windows 10 Version 21H2 for 32-bit Systems Windows 10 Version 21H2 for ARM64-based Systems Windows 10 Version 21H2 for x64-based Systems Windows 10 Version 22H2 for 32-bit Systems Windows 10 Version 22H2 for ARM64-based Systems Windows 10 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for ARM64-based Systems Windows 11 Version 22H2 for x64-based Systems Windows 11 Version 23H2 for ARM64-based Systems Windows 11 Version 23H2 for x64-based Systems Windows 11 Version 24H2 for ARM64-based Systems Windows 11 Version 24H2 for x64-based Systems Windows Server 2008 for 32-bit Systems Service Pack 2 Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) Windows Server 2008 for x64-based Systems Service Pack 2 Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) Windows Server 2008 R2 for x64-based Systems Service Pack 1 Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Ser ver Core installation) Windows Server 2012 Windows Server 2012 (Server Core installation) Windows Server 2012 R2 Windows Server 2012 R2 (Server Core installation) Windows Server 2016 Windows Server 2016 (Server Core installation) Windows Server 2019 Windows Server 2019 (Server Core installation) Windows Server 2022 Windows Server 2022 (Server Core installation) Windows Server 2022, 23H2 Edition (Server Core installation) Windows Server 2025 Windows Server 2025 (Server Core installation) |
| Microsoft Management Console Security Feature Bypass Vulnerability (CVE-2025-26633) | Windows 10 for 32-bit Systems Windows 10 for x64-based Systems Windows 10 Version 1607 for 32-bit Systems Windows 10 Version 1607 for x64-based Systems Windows 10 Version 1809 for 32-bit Systems Windows 10 Version 1809 for x64-based Systems Windows 10 Version 21H2 for 32-bit Systems Windows 10 Version 21H2 for ARM64-based Systems Windows 10 Version 21H2 for x64-based Systems Windows 10 Version 22H2 for 32-bit Systems Windows 10 Version 22H2 for ARM64-based Systems Windows 10 Version 22H2 for x64-based Systems Windows 11 Version 22H2 for ARM64-based Systems Windows 11 Version 22H2 for x64-based Systems Windows 11 Version 23H2 for ARM64-based Systems Windows 11 Version 23H2 for x64-based Systems Windows 11 Version 24H2 for ARM64-based Systems Windows 11 Version 24H2 for x64-based Systems Windows Server 2008 for 32-bit Systems Service Pack 2 Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) Windows Server 2008 for x64-based Systems Service Pack 2 Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) Windows Server 2008 R2 for x64-based Systems Service Pack 1 Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Ser ver Core installation) Windows Server 2012 Windows Server 2012 (Server Core installation) Windows Server 2012 R2 Windows Server 2012 R2 (Server Core installation) Windows Server 2016 Windows Server 2016 (Server Core installation) Windows Server 2019 Windows Server 2019 (Server Core installation) Windows Server 2022 Windows Server 2022 (Server Core installation) Windows Server 2022, 23H2 Edition (Server Core installation) Windows Server 2025 Windows Server 2025 (Server Core installation) |
| Windows Win32 Kernel Subsystem Privilege Escalation Vulnerability (CVE-2025-24983) | Windows 10 for 32-bit Systems Windows 10 for x64-based Systems Windows 10 Version 1607 for 32-bit Systems Windows 10 Version 1607 for x64-based Systems Windows Server 2008 for 32-bit Systems Service Pack 2 Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) Windows Server 2008 for x64-based Systems Service Pack 2 Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) Windows Server 2008 R2 for x64-based Systems Service Pack 1 Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Ser ver Core installation) Windows Server 2012 Windows Server 2012 (Server Core installation) Windows Server 2012 R2 Windows Server 2012 R2 (Server Core installation) Windows Server 2016 Windows Server 2016 (Server Core installation) |
Solutions
Official Solution
Microsoft has released patches for affected software. Affected users can install the corresponding security updates according to the system versions:
Download Links:
1. https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-24993
2. https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-24991
3. https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-24984
4. https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-24985
5. https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-26633
6. https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-24983
Reference
https://msrc.microsoft.com/update-guide/releaseNote/2025-Mar
Timeline
On March 12, 2025, Microsoft released a security bullet.
On March 12, 2025, Sangfor FarSight Labs released a vulnerability alert.





